Introduction
Security defines the success of modern cloud-native deployments. Engineers who master the Certified Kubernetes Security Specialist (CKS) Certification acquire the precise expertise required to shield production clusters from sophisticated exploits. This roadmap guides professionals through a rigorous curriculum at DevOpsSchool to transform them into elite security practitioners. By adopting these hardening techniques, technical leaders ensure their infrastructure remains resilient against the ever-shifting landscape of digital threats.
What is the Certified Kubernetes Security Specialist (CKS) Certification Training Course?
The Certified Kubernetes Security Specialist (CKS) Certification Training Course acts as a high-level validation of an engineer’s capacity to secure a containerized ecosystem. It moves beyond standard orchestration by focusing on the entire software supply chain and the runtime environment. Organizations utilize this certification to identify talent capable of moving security from a peripheral concern to a core operational competency.
Participants in this program tackle real-world scenarios that involve mitigating vulnerabilities within the cluster components and the applications they host. The course forces candidates to demonstrate proficiency in handling API server risks, insecure container images, and host-level kernel threats. Successfully completing this training proves that an individual can build a “Zero Trust” architecture within a Kubernetes framework.
Who Should Pursue Certified Kubernetes Security Specialist (CKS) Certification Training Course?
Senior DevOps professionals, SREs, and Platform Architects who already maintain a solid grasp of cluster administration form the ideal audience for this specialty track. Because the exam mandates an active CKA as a prerequisite, it specifically targets those ready to transition into high-level DevSecOps roles. Engineering managers often pursue this training to better evaluate the security posture of their internal platforms and teams.
Security consultants who are migrating their focus from legacy systems to cloud-native stacks find this course essential for understanding microservices-based attack vectors. In both the Indian and global markets, organizations prioritize specialists who can prove their hands-on ability to harden production environments. Whether you secure financial data or healthcare records, this certification provides the tools needed to maintain rigorous compliance and safety.
Why Certified Kubernetes Security Specialist (CKS) Certification Training Course is Valuable
Modern enterprises face an acute shortage of engineers who can effectively secure automated infrastructure. Obtaining this certification immediately elevates a professional into a niche group of high-value experts, leading to significant career advancement and salary growth. The CKS focuses on the most critical orchestration platform in use today, ensuring that your skills remain relevant as more companies migrate to the cloud.
The true value of this program lies in its ability to reduce the operational attack surface of a company’s infrastructure. Professionals learn to automate threat detection and response, which prevents human error from leading to catastrophic data breaches. This investment secures not only the individual’s career but also the integrity of the entire organization’s digital footprint.
Certified Kubernetes Security Specialist (CKS) Certification Training Course Overview
Engineers access this comprehensive learning path via the Certified Kubernetes Security Specialist (CKS) Certification Training Course hosted on DevOpsSchool. The certification process involves a two-hour, performance-based exam where candidates solve technical security problems in a live command-line environment. The CNCF regularly updates the curriculum to reflect current security patches and the latest container-hardening best practices.
The assessment covers six major domains, including cluster hardening, system security, and runtime monitoring. This performance-centric approach guarantees that every certified specialist possesses the practical skills to solve problems under pressure. By eliminating multiple-choice questions, the program maintains its reputation as one of the most difficult and respected credentials in the tech industry.
Certified Kubernetes Security Specialist (CKS) Certification Training Course Tracks & Levels
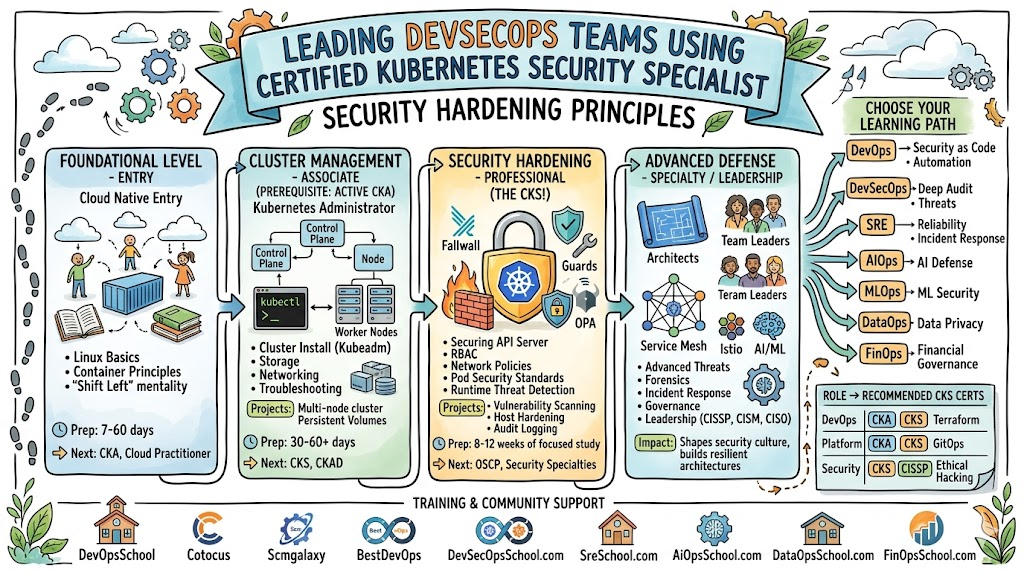
The certification hierarchy provides a logical progression for cloud-native professionals to advance their technical standing. Beginners typically start at the foundational level to grasp the vocabulary and architectural concepts of the CNCF ecosystem. Following this, they move to the associate level, where they gain the hands-on administration experience required for more complex tasks.
The CKS sits at the specialty level, representing the peak of Kubernetes expertise for infrastructure defenders. This level aligns with senior leadership roles that require a deep understanding of both development workflows and operational security. This tiered approach ensures that an engineer builds a comprehensive foundation before tackling the high-stakes world of production security.
Complete Certified Kubernetes Security Specialist (CKS) Certification Training Course Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Cloud Literacy | Foundational | Beginners/Managers | None | K8s Concepts | 1st |
| Administration | Associate | DevOps/SREs | Linux Basics | Cluster Ops | 2nd |
| Security | Specialty | DevSecOps Experts | Valid CKA | Hardening/Audit | 3rd |
| Development | Associate | App Developers | Python/Go/Java | Secure Pod Design | Optional |
Detailed Guide for Each Certified Kubernetes Security Specialist (CKS) Certification Training Course
Foundational Level
Certified Kubernetes Security Specialist (CKS) Certification Training Course – KCNA
What it is
The KCNA validates a professional’s foundational understanding of the cloud-native landscape. It covers the basic mechanics of Kubernetes and the role of various CNCF projects in modern software delivery.
Who should take it
Aspiring cloud engineers, sales professionals, and project managers should start here. It provides the essential context needed to communicate with technical teams and understand the benefits of orchestration.
Skills you’ll gain
- Understanding Kubernetes resource types and their purposes.
- Learning about the CNCF project governance and landscape.
- Grasping basic concepts of cloud-native observability and storage.
- Identifying the benefits of containerization for application scaling.
Real-world projects you should be able to do
- Advise stakeholders on the appropriate cloud-native tools for a project.
- Interpret a high-level architecture diagram of a Kubernetes environment.
Preparation plan
- 7 Days: Study the official CNCF glossary and watch introductory cloud-native webinars.
- 30 Days: Complete an interactive foundational course and pass multiple sample exams.
- 60 Days: Read industry whitepapers focusing on the transition from legacy to cloud-native stacks.
Common mistakes
- Treating the exam as a deep technical test rather than a conceptual one.
- Ignoring the history and role of the Cloud Native Computing Foundation.
Best next certification after this
- Same-track option: CKA (Certified Kubernetes Administrator).
- Cross-track option: PCA (Prometheus Certified Associate).
- Leadership option: Cloud Digital Leader.
Associate Level
Certified Kubernetes Security Specialist (CKS) Certification Training Course – CKA
What it is
The CKA confirms that an individual possesses the skills to manage production-grade Kubernetes clusters. It focuses on the core tasks of installation, configuration, and troubleshooting that administrators perform daily.
Who should take it
System administrators and DevOps engineers who want to prove their operational capability should take this exam. It serves as the primary prerequisite for the more advanced CKS certification.
Skills you’ll gain
- Installing and configuring clusters using the kubeadm tool.
- Solving networking issues between pods and services.
- Managing persistent volumes and storage classes.
- Implementing basic role-based access control (RBAC) within namespaces.
Real-world projects you should be able to do
- Deploy a multi-node Kubernetes cluster and verify its health.
- Perform a rolling upgrade of a cluster with minimal service disruption.
Preparation plan
- 7 Days: Focus on the kubectl command line and imperative resource creation.
- 30 Days: Complete an intensive lab-based training program with simulated exams.
- 60 Days: Experiment with different networking plugins and storage drivers in a test lab.
Common mistakes
- Failing to master a terminal-based text editor like Vim or Nano.
- Neglecting to practice cluster troubleshooting under time constraints.
Best next certification after this
- Same-track option: CKS (Certified Kubernetes Security Specialist).
- Cross-track option: CKAD (Certified Kubernetes Application Developer).
- Leadership option: Certified DevOps Lead.
Professional/Specialty Level
Certified Kubernetes Security Specialist (CKS) Certification Training Course – CKS
What it is
The CKS represents the industry’s highest level of security certification for Kubernetes. It validates the ability to protect the entire stack, from the host operating system to the running application.
Who should take it
Experienced CKA holders and DevSecOps practitioners who want to specialize in infrastructure defense should pursue this. It is the gold standard for those protecting sensitive enterprise data.
Skills you’ll gain
- Hardening the Kubernetes API server and control plane.
- Scanning container images for vulnerabilities during the build phase.
- Implementing runtime security monitoring with tools like Falco.
- Restricting container privileges using Seccomp and AppArmor.
Real-world projects you should be able to do
- Execute a complete security audit of a production-grade cluster.
- Implement a supply chain security pipeline that blocks insecure images.
Preparation plan
- 7 Days: Focus exclusively on third-party security tools like Trivy and Kube-bench.
- 30 Days: Work through advanced security scenarios on platforms like Killer.sh.
- 60 Days: Build and secure multiple clusters using diverse hardening techniques.
Common mistakes
- Underestimating the difficulty of configuring system-level security modules.
- Attempting the exam with an expired CKA certification.
Best next certification after this
- Same-track option: Advanced Cloud Security Architect.
- Cross-track option: HashiCorp Certified Vault Professional.
- Leadership option: CISO track.
Choose Your Learning Path
DevOps Path
The DevOps path focuses on integrating security checks into the automated deployment pipeline. Engineers learn to treat security as an integral part of the CI/CD process, ensuring that every code change undergoes automated hardening. This path balances rapid delivery with infrastructure safety.
DevSecOps Path
Practitioners on this path focus on “Shift Left” security, identifying vulnerabilities at the earliest possible stage of development. They use CKS principles to enforce policy-as-code and ensure that only audited containers reach production. This is the ultimate path for security specialists.
SRE Path
Site Reliability Engineers prioritize system uptime and use security as a pillar of reliability. This path focuses on runtime monitoring and incident response to prevent security breaches from causing system outages. SREs learn to detect and mitigate threats before they impact availability.
AIOps Path
The AIOps path utilizes security telemetry to power intelligent automation systems. Engineers apply CKS auditing techniques to generate data that machine learning models use to predict and block attacks. This path bridges the gap between infrastructure security and data science.
MLOps Path
MLOps professionals use CKS knowledge to secure the sensitive datasets and specialized workloads used in artificial intelligence. They ensure that model training environments remain isolated and that data ingestion pipelines follow strict security protocols. This path protects the organization’s intellectual property.
DataOps Path
The DataOps path focuses on securing data storage and transit layers within a cluster. Specialists learn to implement encryption at rest and secure secrets management for data-intensive applications. This ensures that the data platform meets global privacy and compliance standards.
FinOps Path
FinOps practitioners ensure that cost-saving measures do not introduce security gaps. For example, they learn to secure spot instances and audit the permissions of financial monitoring tools. This path aligns budgetary efficiency with a robust security posture.
Role → Recommended Certified Kubernetes Security Specialist (CKS) Certifications
| Role | Recommended Certifications |
| DevOps Engineer | CKA, CKS, KCNA |
| SRE | CKA, CKS, PCA |
| Platform Engineer | CKA, CKS, Terraform Associate |
| Cloud Engineer | CKA, CKS, Provider Security |
| Security Engineer | CKS, CISSP, CCSP |
| Data Engineer | CKA, CKS, Data Architect |
| FinOps Practitioner | KCNA, FinOps Practitioner |
| Engineering Manager | KCNA, CKA (Foundational) |
Next Certifications to Take After Certified Kubernetes Security Specialist (CKS) Certification Training Course
Same Track Progression
Continue your security journey by earning specialized credentials from cloud providers like AWS, Azure, or GCP. These certifications teach you how to extend Kubernetes security to the surrounding cloud services, such as managed databases and IAM systems. This creates a comprehensive defense strategy for hybrid and multi-cloud environments.
Cross-Track Expansion
Diversify your technical portfolio by mastering service mesh technologies like Istio or Linkerd. A service mesh provides advanced security features like mTLS and fine-grained traffic authorization that complement CKS hardening techniques. This combination makes you an expert in both infrastructure and application-level security.
Leadership & Management Track
Advance into executive roles by pursuing management-focused certifications like the CISM or PMP. These credentials help you translate technical security risks into business terms and manage large-scale compliance projects. You will learn to lead security transformations that align with the strategic goals of the organization.
Training & Certification Support Providers for Certified Kubernetes Security Specialist (CKS) Certification Training Course
- DevOpsSchool: This provider offers an immersive CKS training experience that emphasizes hands-on mastery over theoretical memorization. Their labs mirror the actual exam environment, giving students the confidence to navigate complex security tasks under time pressure. The instructors bring decades of production experience, providing insights into real-world threats and industry-standard hardening techniques. By choosing this school, professionals gain a mentor-led learning journey that bridges the gap between certification and actual career performance.
- Cotocus: This organization specializes in high-intensity training modules for cloud-native security professionals. They focus on the practical implementation of open-source tools like Falco, Trivy, and OPA, ensuring that students can use them in any production setting. Their curriculum stays updated with the latest CNCF exam changes, providing a reliable path for engineers to achieve their certification goals. The flexibility of their learning options makes them a popular choice for busy engineers looking to upskill quickly.
- Scmgalaxy: This platform provides an extensive library of resources and a supportive community for DevOps learners. It serves as a central hub for finding CKS documentation, mock exams, and technical tutorials that simplify complex security concepts. Their modules help candidates break down the CKS syllabus into manageable milestones, ensuring a steady progression toward mastery. It is an excellent resource for anyone looking to supplement their training with community knowledge and shared experiences.
- BestDevOps: This provider focuses on delivering targeted, goal-oriented training that helps candidates pass the CKS exam on their first attempt. Their courses emphasize the most high-weight domains of the exam, such as system hardening and microservice security. With a strong focus on lab work, they ensure that every student can perform the necessary terminal-based tasks with speed and accuracy. Their instructors provide direct feedback on lab performance to help students identify and correct their mistakes early.
- devsecopsschool.com: This institution focuses exclusively on the integration of security into the modern DevOps lifecycle. Their CKS course is part of a broader roadmap that teaches engineers how to implement “Shift Left” security and compliance-as-code. Students learn to handle advanced threats and automate security testing throughout the entire software supply chain. This specialized focus makes them a top choice for those looking to build a dedicated career in the high-demand field of DevSecOps.
- sreschool.com: This training center views security as a critical component of site reliability and infrastructure health. Their CKS curriculum emphasizes runtime monitoring and auditing, helping SREs protect clusters without sacrificing system performance. Students learn to use security data to troubleshoot reliability issues and respond to incidents effectively. This approach is perfect for engineers who manage large-scale, high-availability environments where security and uptime are equally important.
- aiopsschool.com: This provider bridges the gap between infrastructure security and artificial intelligence. Their training shows students how to use CKS auditing logs to feed automated threat-detection systems powered by AI. This forward-thinking approach prepares engineers for the next generation of security operations, where machine learning handles high-volume monitoring. It is a unique path for those who want to lead the adoption of intelligent security automation in their organizations.
- dataopsschool.com: This school focuses on securing the data-intensive workloads that run on Kubernetes. Their CKS training covers the protection of data pipelines, persistent storage, and encrypted secrets management. They help data engineers understand how to maintain strict privacy standards while managing large volumes of information in a containerized environment. This ensures that the data platform remains secure, compliant, and ready for enterprise-level use.
- finopsschool.com: This organization helps engineers align their security hardening efforts with financial accountability. Their training includes modules on securing cost-saving infrastructure like spot instances and auditing the access of financial monitoring tools. Students learn how to optimize cloud spend without creating new security vulnerabilities in their Kubernetes clusters. This holistic view ensures that the organization remains both lean and secure in its cloud operations.
Frequently Asked Questions
1. Is the CKA certification a mandatory requirement for the CKS?
Yes, you must hold an active CKA certification to attempt the CKS exam; otherwise, the Linux Foundation will not issue the credential.
2. How long does the CKS examination session last?
The exam session lasts exactly two hours, requiring you to work quickly and efficiently through a series of technical tasks.
3. What happens if I do not pass the CKS exam on my first try?
The standard exam fee includes one free retake, allowing you to review your mistakes and try again at no extra cost.
4. Can I use external documentation during the performance-based test?
You are permitted to open one additional browser tab to access the official Kubernetes, Falco, or Trivy documentation pages during the exam.
5. What is the passing score for the CKS certification?
You must achieve a score of 67% or higher to pass the exam and receive your Certified Kubernetes Security Specialist badge.
6. Does the CKS exam include multiple-choice questions?
No, the CKS is a 100% performance-based exam where you solve real-world problems in a virtual terminal environment.
7. How long is the CKS certificate valid for before it expires?
The certification remains valid for two years, after which you must recertify to maintain your status as a security specialist.
8. Which Kubernetes version does the current CKS exam use?
The exam typically follows the most recent stable release of Kubernetes and is updated every few months to stay current.
9. Are third-party tools like Falco and Trivy tested in the exam?
Yes, the CKS exam specifically tests your ability to install, configure, and use these tools to secure the cluster.
10. Do I need to be a Linux expert to pass the CKS?
You should have a strong grasp of Linux command-line tools and system-level security, as the exam involves host-level hardening.
11. Is the CKS more difficult than the CKA exam?
Most candidates find the CKS more challenging because it introduces complex security configurations and multiple third-party tools.
12. How should I prepare for the hands-on nature of the exam?
Regularly practicing in lab environments like Killer.sh and setting up your own secure clusters with Kubeadm is the most effective preparation strategy.
FAQs on Certified Kubernetes Security Specialist (CKS) Certification Training Course
1. Which security domain should I prioritize during my study sessions?
Focus heavily on “System Hardening” and “Minimize Microservice Vulnerabilities,” as these domains often represent the largest portion of the exam. You must be comfortable configuring network policies, pod security admission, and host-level security modules like AppArmor. Mastering these areas ensures that you can handle the most high-weight questions that frequently appear on the test.
2. How does the CKS exam test my knowledge of supply chain security?
The exam requires you to demonstrate the ability to scan container images for known vulnerabilities using tools like Trivy and block insecure deployments. You might also need to configure image policy webhooks to ensure that only images from trusted registries can run in the cluster. This validates your ability to protect the cluster from malicious or flawed software from the very beginning.
3. Will I need to configure the Kubernetes API server during the exam?
Hardening the API server is a critical part of the CKS, and you will likely need to disable insecure flags and enable audit logging. You must understand how to configure encryption providers to protect secrets at rest in etcd. These tasks prove that you can secure the control plane, which is the most sensitive part of any Kubernetes environment.
4. What is the role of Falco in the CKS certification process?
Falco is used to test your ability to implement runtime security monitoring and detect suspicious activity inside running containers. You will need to install Falco, configure its rules, and interpret the alerts it generates to identify potential intrusions. This skill is essential for maintaining visibility into the behavior of microservices in a production-grade cluster.
5. How important is the management of Kubernetes Secrets in the curriculum?
The course places a high priority on the secure handling of sensitive information, such as passwords and API keys. You will learn to use RBAC to restrict access to secrets and implement encryption at rest to prevent unauthorized data exposure. These skills are vital for protecting the credentials that your applications use to communicate with other services.
6. Does the exam require knowledge of Admission Controllers?
Yes, you must understand how to use Admission Controllers like the NodeRestriction and PodSecurity to enforce cluster-wide security policies. You may also need to work with Open Policy Agent (OPA) Gatekeeper to implement more complex, custom-defined policies. These tools allow you to automate security and prevent developers from accidentally deploying insecure configurations.
7. How should I manage my time during the two-hour lab exam?
Avoid spending too much time on a single task if you get stuck; move on to other questions and return to the difficult ones later. Use imperative commands to create resources quickly rather than writing extensive YAML files by hand. Efficiency is key, as the performance-based format tests your ability to solve problems accurately and rapidly.
8. Is the CKS certification useful for engineers working on managed services like EKS or GKE?
While the exam focuses on upstream Kubernetes, the security principles you learn are directly applicable to managed services. You will understand what the cloud provider handles for you and what security responsibilities remain your own. This knowledge makes you a more effective architect regardless of which cloud platform your organization chooses to use.
Final Thoughts: Is Certified Kubernetes Security Specialist (CKS) Certification Training Course Worth It?
Mastering the CKS certification provides a definitive edge in the modern, security-conscious technology landscape. It transitions an engineer from a generalist to a specialist capable of defending critical infrastructure against the world’s most advanced threats. For those holding a CKA, this is the most logical and rewarding next step toward a senior-level DevSecOps career. Commitment to this training demonstrates a proactive approach to one of the most significant challenges in tech: infrastructure security. As Kubernetes continues its global expansion, the demand for certified specialists who can prove their skills in the terminal will only increase. If you are ready to take on the challenge, the rewards in terms of career stability, salary, and technical expertise make this journey absolutely worth the effort.
Leave a Reply